Firewall
A method for implementing security policies designed to keep a network secure from intruders. It can be a single router that filters out unwanted packets or may comprise a combination of routers and servers each performing some type of firewall processing. Firewalls are widely used to give users secure access to the Internet as well as to separate a company's public Web server from its internal network. Firewalls are also used to keep internal network segments secure; for example, the accounting network might be vulnerable to snooping from within the enterprise. In practice, many firewalls have default settings that provide little or no security unless specific policies are implemented by trained personnel.
 Firewalls installed to protect entire networks are typically implemented in hardware; however, software firewalls are also available to protect individual workstations from attack. Following are some techniques used in combination to provide firewall protection.
Firewalls installed to protect entire networks are typically implemented in hardware; however, software firewalls are also available to protect individual workstations from attack. Following are some techniques used in combination to provide firewall protection.
- Packet Filter: Blocks traffic based on a specific Web address (IP address) or type of application (e-mail, ftp, Web, etc.), which is specified by port number. Also known as a "screening router."
- Proxy Server: Serves as a relay between two networks, breaking the connection between the two. Also typically caches Web pages.
- Network Address Translation (NAT): Allows one IP address, which is shown to the outside world, to refer to many IP addresses internally; one on each client station. Performs the translation back and forth.
- Stateful Inspection: Tracks the transaction to ensure that inbound packets were requested by the user. Generally can examine multiple layers of the protocol stack, including the data, if required, so blocking can be made at any layer or depth.
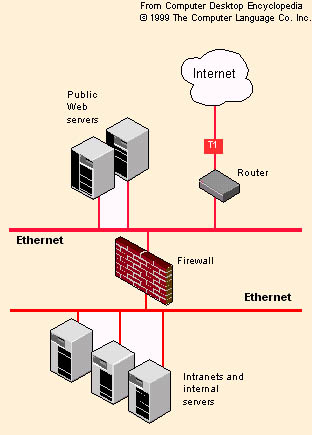
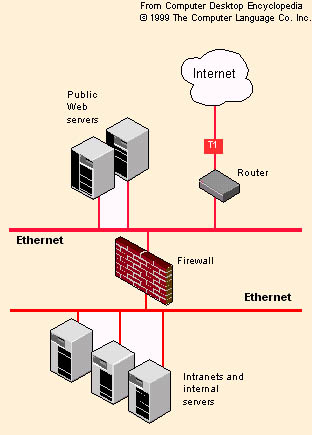
- Firewall Placement: An organization's public Web sites reside outside the firewall, but intranet servers and all internal computing resources are inside the firewall
 Firewalls installed to protect entire networks are typically implemented in hardware; however, software firewalls are also available to protect individual workstations from attack. Following are some techniques used in combination to provide firewall protection.
Firewalls installed to protect entire networks are typically implemented in hardware; however, software firewalls are also available to protect individual workstations from attack. Following are some techniques used in combination to provide firewall protection.